GAO’s IoT security involves safeguarding connected devices and networks in the Internet of Things (IoT). These devices range from everyday household items to sophisticated industrial tools. As IoT devices often have limited processing capabilities and lack standardized security features, they are vulnerable to cyberattacks. Effective IoT security measures include robust encryption, secure authentication protocols, regular software updates, and network segmentation. Implementing these practices helps protect data integrity, ensure device functionality, and prevent unauthorized access. With the proliferation of IoT devices, securing them is paramount to maintaining trust and reliability in modern interconnected systems. As the threat landscape evolves, continuous vigilance and adaptation of security strategies are crucial to defend against emerging cyber threats.
The IoT Security may also be called: Internet of Things Security, IoT Device Protection, Connected Device Security, Smart Device Security, IoT Cybersecurity, IoT Network Security, Internet of Things Protection, Embedded Device Security, Machine-to-Machine (M2M) Security, and IoT Infrastructure Security.
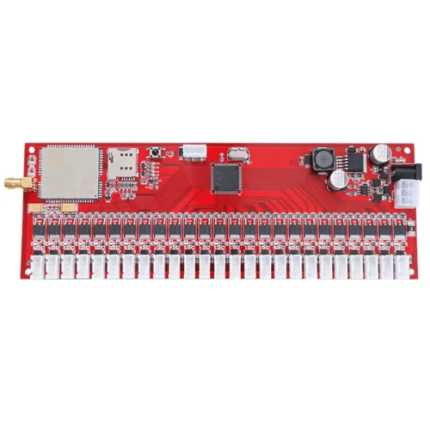
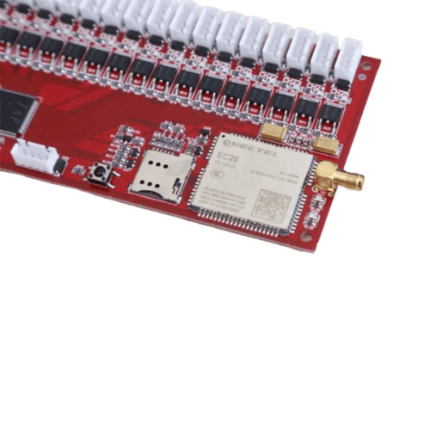
AlertPro-MT7621: User-Friendly SMS Alarm System with High Compatibility – GAOTek
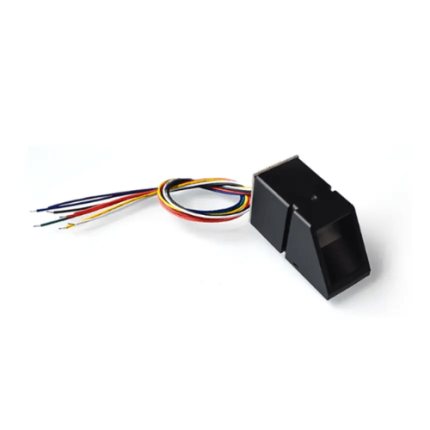
AquaGuard-T1000: Waterproof Fingerprint Sensor with Optical Precision – GAOTek
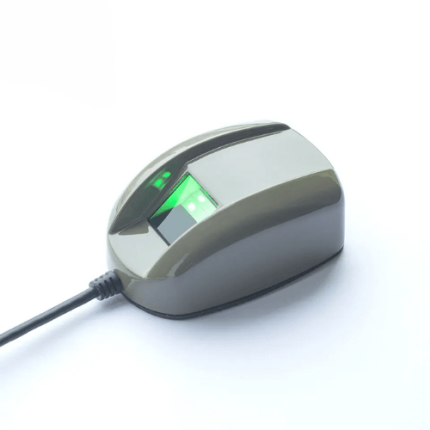
BioGuard-CX5: Advanced Portable Fingerprint Sensor with AES Encryption – GAOTek
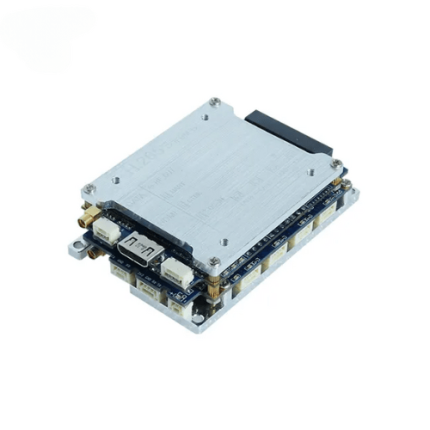
Compact COFDM HD Video Transmitter/Receiver: H.265, AES Encryption, LOS – GAOTek
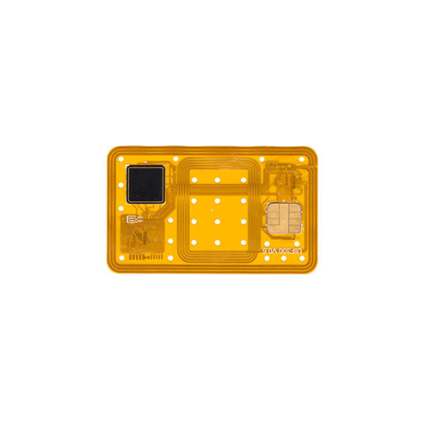
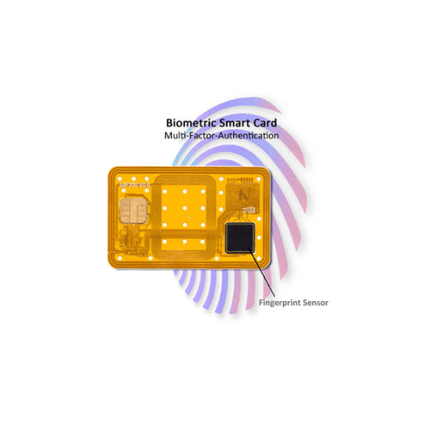
Dual-Interface-Fingerprint Smart Card with 350 dpi Sensor and EMV Test – GAOTek
High-Precision Fingerprint Sensor, Fast Matching, Low Power Consumption – GAOTek
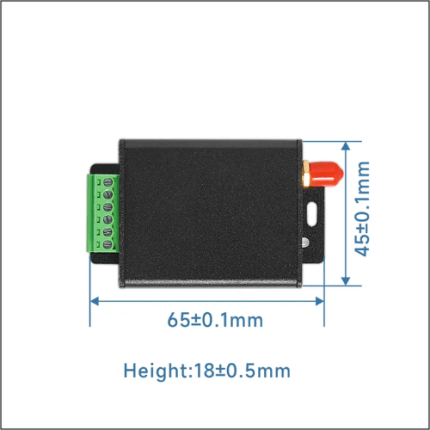
LoRaLink-X500: High-Range Remote Data Collection Module, AES Encryption – GAOTek
NanoPrint-SecureX: Compact Fingerprint Scanner with AES Encryption, USB – GAOTek
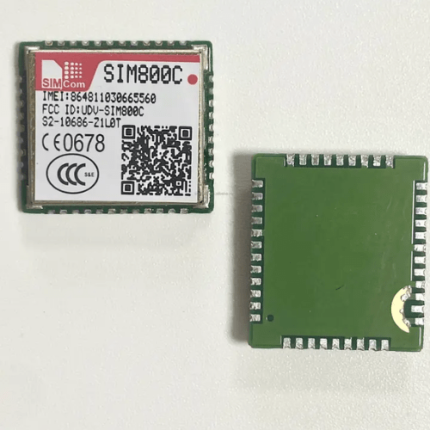
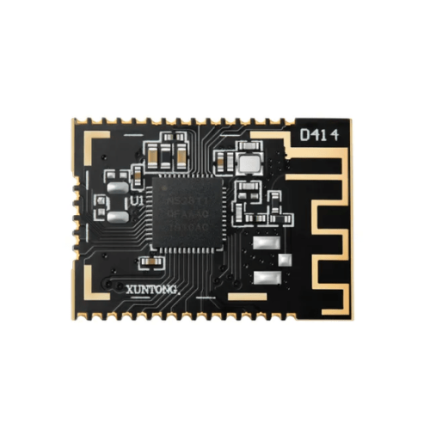
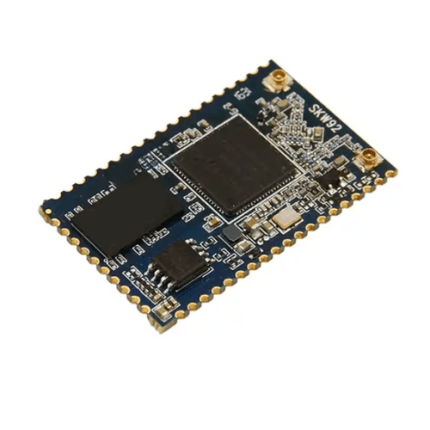
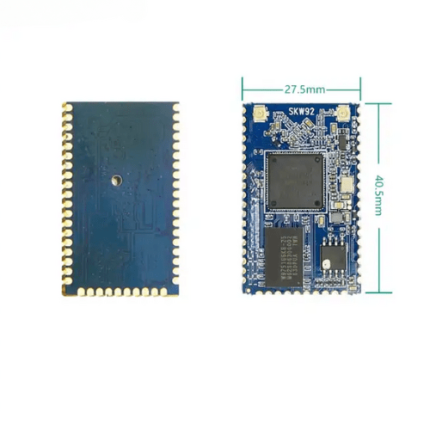
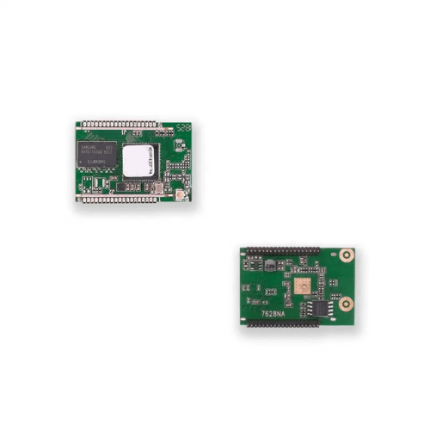
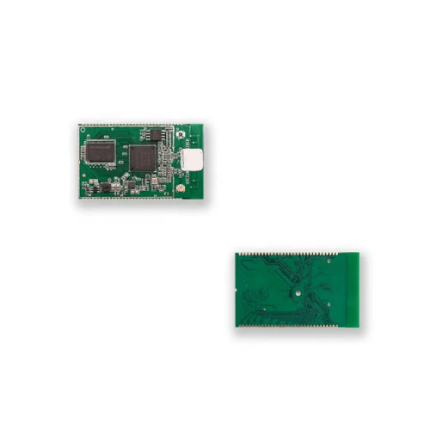
NetMatch-MT: Compact IEEE 802.11 Wireless Module with Advanced Security – GAOTek
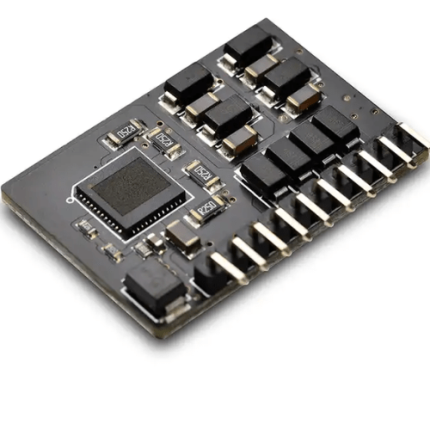
Precise EcoPoE-Mini: Cost-Effective PoE Module with Minimal Components – GAOTek
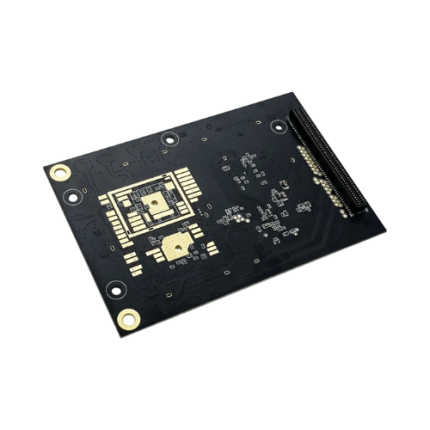
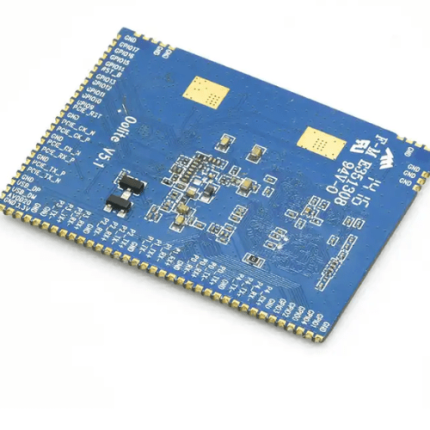
SecureGuard-CM4: Waterproof ARM Processor with Encryption, Protection – GAOTek
GAO’s IoT Security is composed of following components:
- Authentication and Authorization
- Encryption
- Network Security
- Secure Firmware and Software Updates
- Device Management
- Data Privacy
- Physical Security
- Threat Detection and Response
- Incident Management
- Compliance and Risk Management
GAO Tek’s IoT Security has the following functions:
- Authentication and Authorization: GAO’s IoT security functions ensure that only authorized users and devices can access the network and its resources, verifying identities and managing access levels.
- Data Encryption: We implement robust encryption protocols to protect data as it travels across networks, making it unreadable to unauthorized parties and safeguarding sensitive information.
- Network Protection: Our solutions focus on securing communication channels through firewalls, intrusion detection systems, and network segmentation to prevent unauthorized access and attacks.
- Firmware and Software Updates: GAO Tek ensures that devices receive timely updates and patches to address vulnerabilities, maintaining security as threats evolve.
- Device Management: We handle the lifecycle of IoT devices, including monitoring, configuration, and management to ensure they remain secure and functional.
- Privacy Controls: GAO’s security framework emphasizes protecting user data and ensuring compliance with privacy regulations to prevent unauthorized data access.
- Physical Security Measures: Our approach includes securing the physical components of IoT devices against tampering and theft, employing measures like secure enclosures and tamper-evident technologies.
- Threat Detection and Response: We provide continuous monitoring and rapid response to suspicious activities, minimizing potential security breaches and mitigating risks.
- Incident Management: GAO’s protocols ensure effective identification, management, and recovery from security incidents, aiming to minimize impact and restore normal operations swiftly.
- Compliance and Risk Management: We ensure adherence to industry standards and regulations, assessing and managing risks associated with IoT deployments to protect our clients and their assets.
GAO Tek’s IoT Security comply with applicable industry standards such as:
- ISO/IEC 27001
- ISO/IEC 27032
- NIST SP 800-53
- NIST SP 800-213
- IEC 62443
- GDPR
- PCI DSS
- HIPAA
- FIPS 140-2
- IoT Cybersecurity Improvement Act
Our IoT Security help our customers comply with relevant U.S. government regulations such as:
- IoT Cybersecurity Improvement Act
- Federal Information Security Management Act (FISMA)
- Health Insurance Portability and Accountability Act (HIPAA)
- Gramm-Leach-Bliley Act (GLBA)
- Federal Trade Commission Act (FTC Act)
- Payment Card Industry Data Security Standard (PCI DSS)
- Controlled Unclassified Information (CUI) Regulations
- NIST Cybersecurity Framework
- FIPS 140-2
- Executive Order on Improving the Nation’s Cybersecurity
Our IoT Security help our clients comply with relevant Canadian government regulations such as:
- Personal Information Protection and Electronic Documents Act (PIPEDA)
- Privacy Act
- Canadian Anti-Spam Legislation (CASL)
- Communications Security Establishment (CSE) Directive
- Government of Canada’s IT Security Policy
- Canadian Standards Association (CSA) Cybersecurity Standards
- Digital Privacy Act
- Framework for Critical Infrastructure Protection (CIIP)
- Canadian Centre for Cyber Security Guidelines
- Information Security Management Framework (ISMF)
Our IoT Security have the following applications:
- Smart Home Devices: GAO’s IoT security solutions protect smart home devices, such as thermostats and security cameras, ensuring safe and private home automation.
- Industrial Automation: We implement security measures to safeguard industrial IoT systems, preventing unauthorized access and protecting critical infrastructure from cyber threats.
- Healthcare: Our IoT security strategies ensure the protection of connected medical devices and patient data, complying with regulatory standards and maintaining data integrity.
- Smart Cities: GAO Tek secures various smart city applications, including traffic management systems and public safety networks, enhancing the safety and efficiency of urban environments.
- Agriculture: We protect IoT systems used in precision farming, ensuring secure data transmission and operational safety for automated agricultural equipment.
- Supply Chain Management: GAO’s solutions provide security for IoT-based logistics and inventory systems, safeguarding sensitive data and preventing disruptions.
- Energy Management: Our security measures protect smart grids and energy management systems from cyber threats, ensuring reliable and secure energy distribution.
- Retail: We secure IoT devices used in retail environments, such as point-of-sale systems and inventory tracking, to protect customer information and prevent fraud.
- Transportation: GAO’s IoT security solutions enhance the safety of connected vehicles and transportation systems, preventing unauthorized access and ensuring operational integrity.
- Environmental Monitoring: We secure IoT systems used for monitoring environmental conditions, protecting data from tampering and ensuring accurate and reliable reporting.
Below are our resource pages containing useful information on IoT Security:
FAQs on IoT Security on GAOTek.com
How to Choose an IoT Security
Components of IoT Security
Operation, Maintenance & Calibration of IoT Security
Customers in the U.S and Canada of IoT Security
Applications of IoT Security in Educational Services
Our IoT Security are in stock and can be shipped overnight within the continental U.S. and Canada from a nearby warehouse in the U.S. or Canada, and can also be shipped globally.
We provide 24/7 support. If you have any questions, our technical experts can help you. Please fill out this form or email us.